Linux 下手动查杀木马过程

- 模拟木马程序病原体并让木马程序自动运行
- 黑客让脚本自动执行的 3 种方法:
(1)、计划任务: crontab
(2)、开机启动
(3)、系统命令被人替换,定一个触发事件 - 生成木马程序病原体
vim /usr/bin/troy
!/bin/bash
touch /tmp/aaa.txt
while true
do
echo `date` >> /tmp/date.txt
sleep 1
done - chmod +x /usr/bin/troy
troy &
[1] 19273
ps -aux|grep troy

- 使用计划任务 crontab 让木马自动运行
- crontab -e
00 00 * * * /usr/bin/troy &
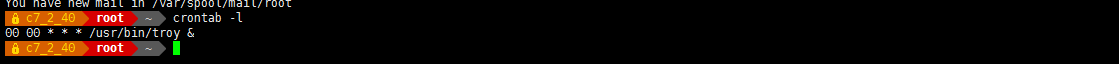
- 黑客以非 root 用户添加计划任务,最好使用已经存在系统用户添加。这里使用 bin 用户来添加
- crontab -u bin -e
1 * * * * echo "aaaaaaa" >> /tmp/bin.txt
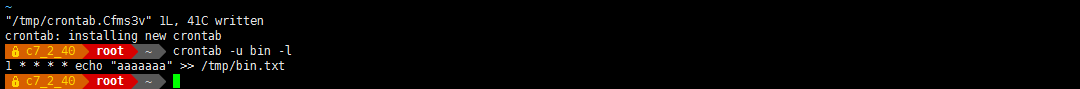
- 如何查看所有用户的计划任务? 做黑客要有一个很扎实的基础,还要有一个很好的思维。不用遍历/etc/passwd 中所有的文件,这太复杂了。因为每个用户的计划任务都有独立的文件。
ll /var/spool/cron/ 这个目录下存放着所有用户级别的计划任务
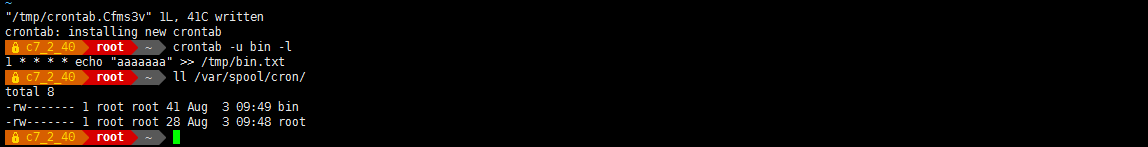
- 注:所有用户的计划任务,都会在/var/spool/cron/下产生对应的文件。只要看一下这个目录下的文件,就知道哪些用户生成了计划任务
- 黑客使在系统级别的计划任务中追加木马 ,查看系统级别的计划任务相关文件
- ls /etc/cron*

- 注:
crontab 写具体时间的统级别的定时任务
cron.d/ 系统级别的定时任务
cron.daily/ 系统每天要执行计划任务
cron.hourly/ 系统每小时要执行计划任务
cron.monthly/ 系统每月要执行计划任务
cron.weekly/ 系统每周要执行计划任务 - 系统级别的计划任务
vim /etc/crontab 在最后追加
01 3 * * * root /bin/workstat &
添加系统级别的木马程序。可以追加到系统自带的脚本中,也可以自己新创建一个脚本,放到对应的目录下

- vim /etc/cron.daily/logrotate 在最后添加/usr/bin/troy &
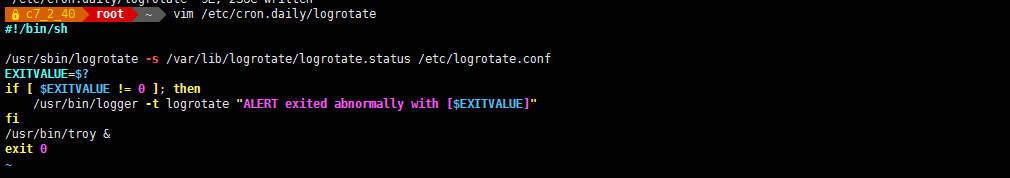
- 测试执行:
/etc/cron.daily/logrotate 可以执行,这样木马就可以随着 tmpwatch 执行了

-
排查:利用 md5sum ,来检验文件的完整性
语法:md5sum 文件 - md5sum /etc/cron.daily/logrotate
0ba7f606f28e9366fd7ceba7e95a17bb /etc/cron.daily/logrotate
echo "test" >> /etc/cron.daily/logrotate
md5sum /etc/cron.daily/logrotate
f808a2378eb80771d510a5fade7b800c /etc/cron.daily/logrotate
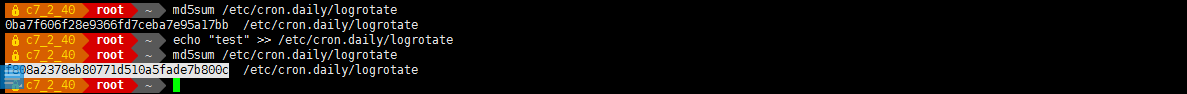
- 注:所以通过对比 MD5 值,可以发现文件内容发生了变化。另外,系统级别的计划任务,从安装好系统后,就固定下来,一般情况不会发生改变。
- 如何排查/etc/cron*下所有文件有没有被黑客修改或追加?
思路:对所有文件都生成一个 md5 值库,后期进行对比,可以快速找出被修改的文件。
例: 对/etc/cron*下所有文件都生成 md5 值,保存为一个 md5 值的文件 - find /etc/cron* -type f -exec md5sum {} \; > /opt/file_md5.v1
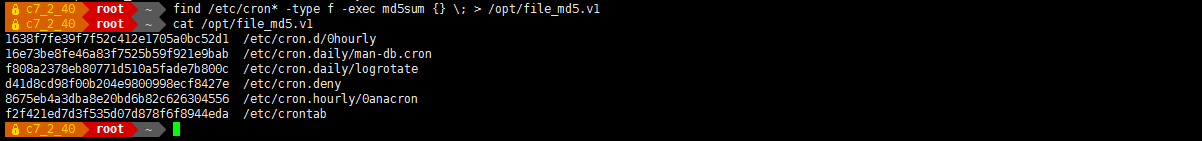
- 模拟黑客在文件的最后添加以下选中的内容
- echo 123456 /etc/cron.daily/logrotate
- 当发现服务器异常时,生成一个新的 MD5 值库
find /etc/cron* -type f -exec md5sum {} \; > /opt/file_md5.v2
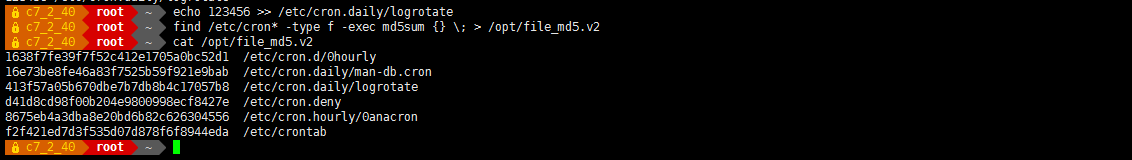
- 使用 diff 对2个文件进行对比
- diff /opt/file_md5.v1 /opt/file_md5.v2

- 注:如果没有前生成 file_md5.v1 怎么办?
找一台正常和你服务器系统版本号一样的虚拟机,在虚拟机中生成 md5 值数据库文件。复制到服务器上,再对比。
- 通过开机启动脚本运行木马 /etc/rc.local 这个是开机启动脚本
- echo "troy" >> /etc/rc.local

- 特例:很多人 vim 打开一个文件后,看到文档的后面是一片空白,就认为是达到文件的最后了。所以黑客在/etc/rc.local 中添加很多空行,然后在文档最后添加木马程序, 再把光标移动到行首,保存退出。也可以躲避一些运维人员的视线,达到隐藏木马的目的。
- 排查:过滤掉空行
egrep -v "^$" /etc/rc.local
参数说明: ^$ 表示找出以$结束符开头的行,即空行; -v 表示取反显示

- 把木马程序脚本写到已经存在的开机启动服务中,例如:network
-
vim /etc/init.d/network
! /bin/bash
network Bring up/down networking
chkconfig: 2345 10 90
Source function library.
. /etc/init.d/functions
/usr/bin/troy & 添加这行

- 测试

- 更强的黑客:自己写一个开机启动程序
- vim /etc/init.d/troy
!/bin/bash
chkconfig: 12345 90 90
description: troy
END INIT INFO
case $1 in
start)
/usr/bin/troy &
;;
stop)
;;
*)
/usr/bin/troy &
;;
esac

- 重启验证

- 查看每个系统级别下的启动脚本
- ll /etc/rc*/* | grep troy

- 删除木马方法

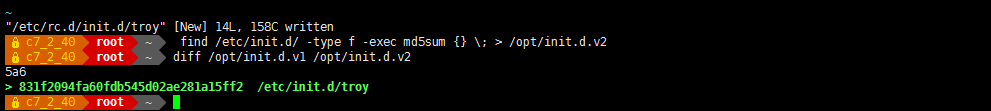
- 排查: 对比法
- find /etc/init.d/ -type f -exec md5sum {} \; > /opt/init.d.v1

- find /etc/init.d/ -type f -exec md5sum {} \; > /opt/init.d.v2
diff /opt/init.d.v1 /opt/init.d.v2
- 排查方法总结
方法 1:对比其他服务器的正常配置文件 ,利用 MD5 值做对比
方法 2: 查看被黑当天生成或被修改的文件 - 查看前一天(24小时内)到现在被修改过的文件

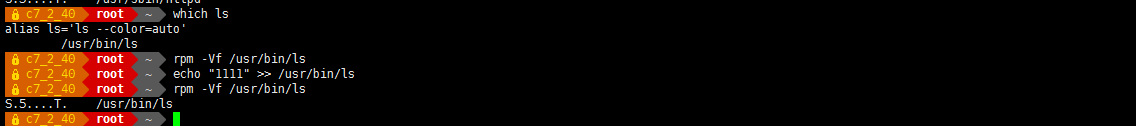
- 使用 rpm 检查文件的完整性
语法:rpm -V 软件包的名字 使用 rpm 命令检查软件包安装后,生产的所有的文件的完整性
语法:rpm -Vf 命令的绝对路径 使用 rpm 检查命令的完整性

- rpm -V 弹出的每列消息含意如下:
S file Size 大小不一致
MMode 模式不一致 (包括许可和文件类型)
5 MD5 sum 校验和不一致
DDevice 主从设备号不匹配
L readLink(2) 路径不匹配
UUser 属主不一致
GGroup 所属组不一致
T mTime 修改时间不一致 - 查看命令有没有被修改
which ls
/usr/bin/ls
rpm -Vf /usr/bin/ls
echo aaaa >> /usr/bin/ls 模拟黑客,修改这个文件
rpm -Vf /usr/bin/ls 检查文件,弹出消息,说明文件内容被修改了
- 系统中有很多命令和软件包,如何校对所有的命令和包?
查看所有 rpm 安装的软件包,生成命令或文件是否被改过?
例:rpm -Va > rpm_check.txt 时间较长

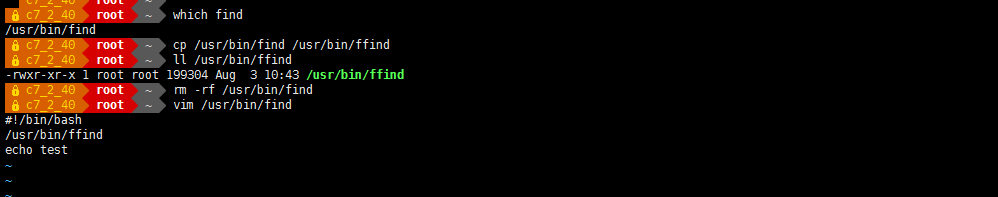
- 系统命令被人替换
黑客修改/替换系统命令 , 查看命令有没有被修改
which find
/usr/bin/find
cp /usr/bin/find /usr/bin/ffind
rm -rf /usr/bin/find 删除原来的 find
vim /usr/bin/find 插入以下内容
!/bin/bash
/usr/bin/ffind
echo test
chmod +x /usr/bin/find
测试:
find /opt 没有报错,说明木马执行成功。

- 总结:
黑客如何让脚本定时执行,有以下三种方法:
1、计划任务: crontab 和系统级别的计划任务
2、开机启动 rc.local 和开机启动脚本
3、系统命令被人替换,定一个触发事件
排查木马方法总结:
方法 1:通过生成 md5 值数据库,查询文件系统的完整性
方法 2: 利用 find 命令查找下最近被修改过的文件:一般情况下命令文件都很久之前被修改的。
方法 3: 被入侵后,检测所有 rpm -Va 生成的文件是否被改动过

- 生成木马程序的父进程脚本
- vim /bin/workstat 写一个木马程序的父进程,用于检测木马运行的脚本。
!/bin/bash
while true
do
num=`pgrep troy|wc -l`
if [[ $num -le "1" ]]; then
/bin/cp /usr/troyold /usr/bin/troy &> /dev/null
/usr/bin/troy &
fi
done
service network restart &> /dev/null

- 测试 木马被删除后自动运行

- 删除木马父进程
排查思路:这种情况下,你需要把找到木马的父进程,把父进程删除,再把病毒的原体删除 - pstree | grep troy
| | `-workstat---2*[troy---sleep] - 查看父进程
- ps -axu | grep workstat
root 23054 0.0 0.0 112828 2276 pts/0 S+ 11:19 0:00 grep --color=auto workstat
root 89583 5.0 0.0 113304 2860 pts/0 S 11:16 0:08 /bin/bash /usr/bin/workstat - 让进程停止运行,不是杀掉。 如果直接杀死子进程,会再产生新进程,这里把进程停止,让进程不在发挥攻击作用,然后你自己再慢慢排查
- 或者直接杀掉父进程,再杀死 子进程
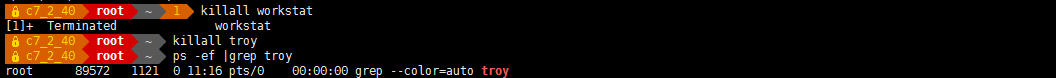

- S 表示是 sleep 状态 R 表示正在运行 Z 表示 僵尸进程 T 表示停止运行

- 先杀死 父进程 再杀死子进程

- 删除 父进程 文件 再删除 子进程文件

-
创建一个让 root 用户都删除不了的木马程序
- chattr 扩展权限说明
+i:即 Immutable,系统不允许对这个文件进行任何的修改。如果目录具有这个属性,那么任何的进程只能修改目录之下的文件,不允许建立和删除文件。 注:immutable [ɪˈmju:təbl] 不可改变的
-i :移除 i 参数。 - 如果工作中发现某个木马程序不停的运行,可以利用扩展属性,让木马程序没有可执行权限。
touch /bin/workstat
chmod 0000 /bin/workstat && chattr +i /bin/workstat
-
不让木马程序和外网数据主动通信
- 木马需要对外发大量数据包,管理可以通过 iptables 在 output 链上做限制,比如,把从output 链出去 state 状态为 new 的全部 drop 掉。
iptables -t filter -A OUTPUT -m state --state NEW -j DROP - 注:这是基于状态的防火墙规则。 由服务器自己自动发起的 TCP 链接状态为 NEW。木马程序一般都是主动发启连接的。
- 当然,黑客也可以在/bin/workstat 脚本中,添加放行木马通信的规则,如下:
iptables -F OUTPUT
iptables -t filter -A OUTPUT -m state --state NEW -j ACCEPT
这样木马就可以上网了。
-
检查 rootkit
-
使用 rkhunter Rootkit 猎手来检查 rootkit
-
rkhunter 概述:中文名叫”Rootkit 猎人”, rkhunter 是 Linux 系统平台下的一款开源入侵检测工具,具有非常全面的扫描范围,除了能够检测各种已知的 rootkit 特征码以外,还支持端口扫描、常用程序文件的变动情况检查。
-
注: 在 centos7 下的 epel 源中有 rkhunter 安装包, 在 centos7 上使用这个来检查rootkit 。
-
安装 rkhunter 和 unhide 包
rkhunter.noarch 用于扫描 rootkit 和本地提权漏洞
unhide.x86_64 用于找到隐藏的进程和 TCP / UDP 后门端口
yum install epel-release -y 安装 epel 源
yum install rkhunter unhide -y

- 为基本系统程序建立校对样本,建议系统安装完成后,马上建立校对样本。
rkhunter --propupd - 查看存储样本文件的数据库
- ll /var/lib/rkhunter/db/
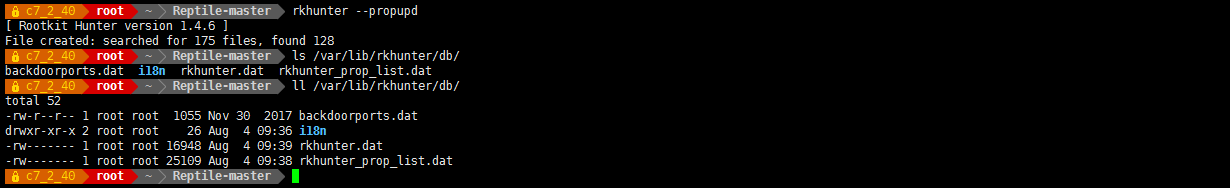
- grep passwd /var/lib/rkhunter/db/rkhunter.dat
File:0:/usr/bin/passwd:0942cd4ffd8ad68821b0d07060c713c6bf5d6643201a450b9a0511a4369ea919:100946882:04755:0:0:27856:1585713439:passwd:0:: - 运行 rkhunter 检查系统
rkhunter 主要执行下面一系列的测试:
(1). MD5 校验测试, 检测任何文件是否改动.
(2). 检测 rootkits 使用的二进制和系统工具文件.
(3). 检测特洛伊木马程序的特征码.
(4). 检测大多常用程序的文件异常属性.
(5). 执行一些系统相关的测试 - 因为 rootkit hunter 可支持多个系统平台.
(6). 扫描任何混杂模式下的接口和后门程序常用的端口.
(7). 检测如/etc/rc.d/目录下的所有配置文件, 日志文件, 任何异常的隐藏文件等等.
(8). 对一些使用常用端口的应用程序进行版本测试. 如: Apache Web Server, Procmail 等. - echo aaaaaa >> /usr/sbin/useradd 模拟黑客修改命令
- 执行检测命令
rkhunter --check -sk 注: --sk 遇到需要按 enter 的地方,直接跳过 --skip-keypress第一部分:检测系统命令,主要检测系统的二进制文件,这些文件最容易被rootkit攻击;
[ OK ]表示正常,[ Warning ]表示有异常,[ None found ]未找到

- 第二部分:检测rootkit,主要检测常见的rootkit程序;
[ Not found ]表示未感染

- 第三部分:特殊或附加检测:对rootkit文件或目录检测、对恶意软件检测、对指定内核检测等

- 第四部分:检测网络、系统端口、系统启动文件、系统用户和组配置、ssh配置、文件系统等


- 第五部分:应用程序版本检测

System checks summary
=====================
File properties checks...
Files checked: 128
Suspect files: 3
Rootkit checks...
Rootkits checked : 486
Possible rootkits: 0
- 使用计划任务每日自动检测
- mkdir /root/.rkhunter
- chmod -R 700 /root/.rkhunter
- crontab -l
00 00 * * * /usr/bin/rkhunter --check --sk > /root/.rkhunter/check.txt

- 在线升级
- rkhunter 是通过一个含有 rootkit 名字的数据库来检测系统的 rootkits 漏洞, 所以经常更新该数据库非常重要, 通过下面命令来更新该数据库:
rkhunter --update

- 检测最新版本
rkhunter --versioncheck - 总结:使用 rkhunter 的检测之后发现很多被黑客修改的地方后,处理被黑的服务器步骤如下:
(1).将原主机的网络线拔除,使用内网排查;
(2).备份数据,把重要的服务安装文件和数据备份;
(3).查看备份的数据中有没有怪异的文件,可以下载本地,使用 windows 中的杀毒软件,查一下
(4).重新安装一部完整的系统,使用 yum update 更新系统到最新版本
(5). 使用 nessus 之类的软件,检验系统是否处在较为安全的状态
(6).将原本的重要数据移动至上个步骤安装好的系统当中,并启动原本服务器上面的各项服务;
(7).配置防火墙的规则
(8).最后,将原本完整备份的数据拿出来进行分析,尤其是 logfile 部分,试图找出黑客是由那个
服务?那个时间点? 以那个远程 IP 联机进入本机等等的信息,并针对该信息研拟预防的方法,并应用在已经运作的机器上。
-
使用 Tripwire 检查文件系统完整性
- Tripwire 是目前最为著名的 unix 下文件系统完整性检查的软件工具,这一软件采用的技术核心就是对每个要监控的文件产生一个数字签名,保留下来。当文件现在的数字签名与保留的数字签名不一致时,那么现在这个文件必定被改动过了。
- Tripwire 可以对要求校验的系统文件进行类似 md5 的运行,而生成一个唯一的标识,即“快照”snapshot。当这些系统文件的大小、inode 号、权限、时间等任意属性被修改后,再次运行Tripwire,其会进行前后属性的对比,并生成相关的详细报告。
- yum install epel-release
安装 Tripwire,使用 yum:
yum install tripwire -y

- 配置 Tripwire
这一步使用密码为 Tripwire 生成一个站点(site)密钥和一个本地(local)密钥。这可以帮助保护Tripwire 免受未经授权的访问。本地密钥用于数据库文件,站点密钥用于配置文件和策略文件。您需要记住自己给出的密码,因为您更新策略文件或数据库时需要输入这些密码。下面的命令生成密钥:
tripwire-setup-keyfiles 密码都是 123456----------------------------------------------
The Tripwire site and local passphrases are used to sign a variety of
files, such as the configuration, policy, and database files.Passphrases should be at least 8 characters in length and contain both
letters and numbers.See the Tripwire manual for more information.
----------------------------------------------
Creating key files...(When selecting a passphrase, keep in mind that good passphrases typically
have upper and lower case letters, digits and punctuation marks, and are
at least 8 characters in length.)Enter the site keyfile passphrase:
Verify the site keyfile passphrase:
Generating key (this may take several minutes)...Key generation complete.(When selecting a passphrase, keep in mind that good passphrases typically
have upper and lower case letters, digits and punctuation marks, and are
at least 8 characters in length.)Enter the local keyfile passphrase:
Verify the local keyfile passphrase:
Generating key (this may take several minutes)...Key generation complete.----------------------------------------------
Signing configuration file...
Please enter your site passphrase:
Wrote configuration file: /etc/tripwire/tw.cfgA clear-text version of the Tripwire configuration file:
/etc/tripwire/twcfg.txt
has been preserved for your inspection. It is recommended that you
move this file to a secure location and/or encrypt it in place (using a
tool such as GPG, for example) after you have examined it.
----------------------------------------------
Signing policy file...
Please enter your site passphrase:
Wrote policy file: /etc/tripwire/tw.polA clear-text version of the Tripwire policy file:
/etc/tripwire/twpol.txt
has been preserved for your inspection. This implements a minimal
policy, intended only to test essential Tripwire functionality. You
should edit the policy file to describe your system, and then use
twadmin to generate a new signed copy of the Tripwire policy.Once you have a satisfactory Tripwire policy file, you should move the
clear-text version to a secure location and/or encrypt it in place
(using a tool such as GPG, for example).Now run "tripwire --init" to enter Database Initialization Mode. This
reads the policy file, generates a database based on its contents, and
then cryptographically signs the resulting database. Options can be
entered on the command line to specify which policy, configuration, and
key files are used to create the database. The filename for the
database can be specified as well. If no options are specified, the
default values from the current configuration file are used. -
tripwire --init 初始化数据库:生成基准数据库
Wrote database file: /var/lib/tripwire/c7_2_40.twd 存储数据的路径及文件名
The database was successfully generated.
-
配置 Tripwire 策略
vim /etc/tripwire/twpol.txt 一般不需要修改,默认就可以了

c7_2_40-local.key 加密本地密钥文件
site.key 加密站点密钥文件
tw.cfg 加密配置变量文件
tw.pol 加密策略文件
twcfg.txt 定义数据库、策略文件和 Tripwire 可执行文件的位置
twpol.txt 定义检测的对象及违规时采取的行为
- 测试
- 添加或修改一些文档
echo aaa >> /etc/passwd
useradd gf1 添加一个用户名为 gf1 的用户 - 第一次完整性检查,和常用检查参数
tripwire --check 可以发现以下内容被修改了

- 示例及用法
只检查指定的文件或目录
tripwire --check /etc/passwd
tripwire --check /etc/ - 升级基准数据库文件
升级的目的是很正常的,因为 check 是基于基准数据的
tripwire --init - 在 /var/lib/tripwire/report 目录中,Tripwire 生成的所有报告文件都是hostname<date_stamp>.twr 形式的。通过按日期顺序列出文件,简单地选择这次 Tripwire 扫描生成的报告。一旦有了正确的文件,就可以使用下面这个命令更新数据库:
- tripwire --update --twrfile /var/lib/tripwire/report/c7_2_40-20210804-102714.twr
- 执行该命令之后,您就进入了一个编辑器。搜索所报告的文件名。所有侵害或更新都在文件名前面有一个 [x]。该演示中的查找模式如下:
[x] "/etc/passwd"
如果您希望接受这些更改为正当的,则只需保存并退出文件即可。Tripwire 不再报告此文件。如果您想要这个文件不被添加到数据库,那么请删除 'x'。
保存文件并退出编辑器时,若有数据库更新发生,会提示您输入密码以完成该过程。如果没有更新发生,那么 Tripwire 会通知您的,并且不需要输入密码。 - tripwire --update --twrfile /var/lib/tripwire/report/c7_2_40-20210805-100010.twr

黑客运行木马原理:
1、生成是病原体
2、通过脚本每隔 1 分钟自动检测一次,如果木马程序不存在,就从病原体复制一份儿到某个目录,
然后执行副本木马,生成一个随机命名的程序。把副本放到系统计划任务多个路径下
3、修改自启动配置 chkconfig --add xxx
4、修改自启动项/etc/rc.local
排查解决方法:
1、删除病原体以及其副本
2、删除系统计划任务中可疑的程序
3、删掉自启动服务的脚本 chkconfig --del xxx
4、删掉可疑的自启动项:vi /etc/rc.local
5、删除/etc/crontab 下可疑的任务
6、删除/etc/cron*下可疑的 sh 脚本
7、重启,查看脚本是否还执行
网站声明:如果转载,请联系本站管理员。否则一切后果自行承担。
- 上周热门
- 如何使用 StarRocks 管理和优化数据湖中的数据? 2944
- 【软件正版化】软件正版化工作要点 2863
- 统信UOS试玩黑神话:悟空 2823
- 信刻光盘安全隔离与信息交换系统 2717
- 镜舟科技与中启乘数科技达成战略合作,共筑数据服务新生态 1251
- grub引导程序无法找到指定设备和分区 1217
- 华为全联接大会2024丨软通动力分论坛精彩议程抢先看! 163
- 点击报名 | 京东2025校招进校行程预告 162
- 2024海洋能源产业融合发展论坛暨博览会同期活动-海洋能源与数字化智能化论坛成功举办 160
- 华为纯血鸿蒙正式版9月底见!但Mate 70的内情还得接着挖... 157
- 本周热议
- 我的信创开放社区兼职赚钱历程 40
- 今天你签到了吗? 27
- 信创开放社区邀请他人注册的具体步骤如下 15
- 如何玩转信创开放社区—从小白进阶到专家 15
- 方德桌面操作系统 14
- 我有15积分有什么用? 13
- 用抖音玩法闯信创开放社区——用平台宣传企业产品服务 13
- 如何让你先人一步获得悬赏问题信息?(创作者必看) 12
- 2024中国信创产业发展大会暨中国信息科技创新与应用博览会 9
- 中央国家机关政府采购中心:应当将CPU、操作系统符合安全可靠测评要求纳入采购需求 8

